What decision-makers should know
Mid-market IT teams and MSPs are squeezed by rising infrastructure costs, shorter refresh cycles, and heavier compliance requirements — all while Kubernetes and containerized workloads push operational models toward declarative, ephemeral infrastructure. The immediate operational problem isn’t just more data; it’s that the storage lifecycle (provisioning, protection, retention, reclamation) remains largely manual and decoupled from the manifests and GitOps workflows we use to manage applications. That gap creates overprovisioning, orphaned volumes, audit blind spots, and unexpected CapEx/OpEx spikes.
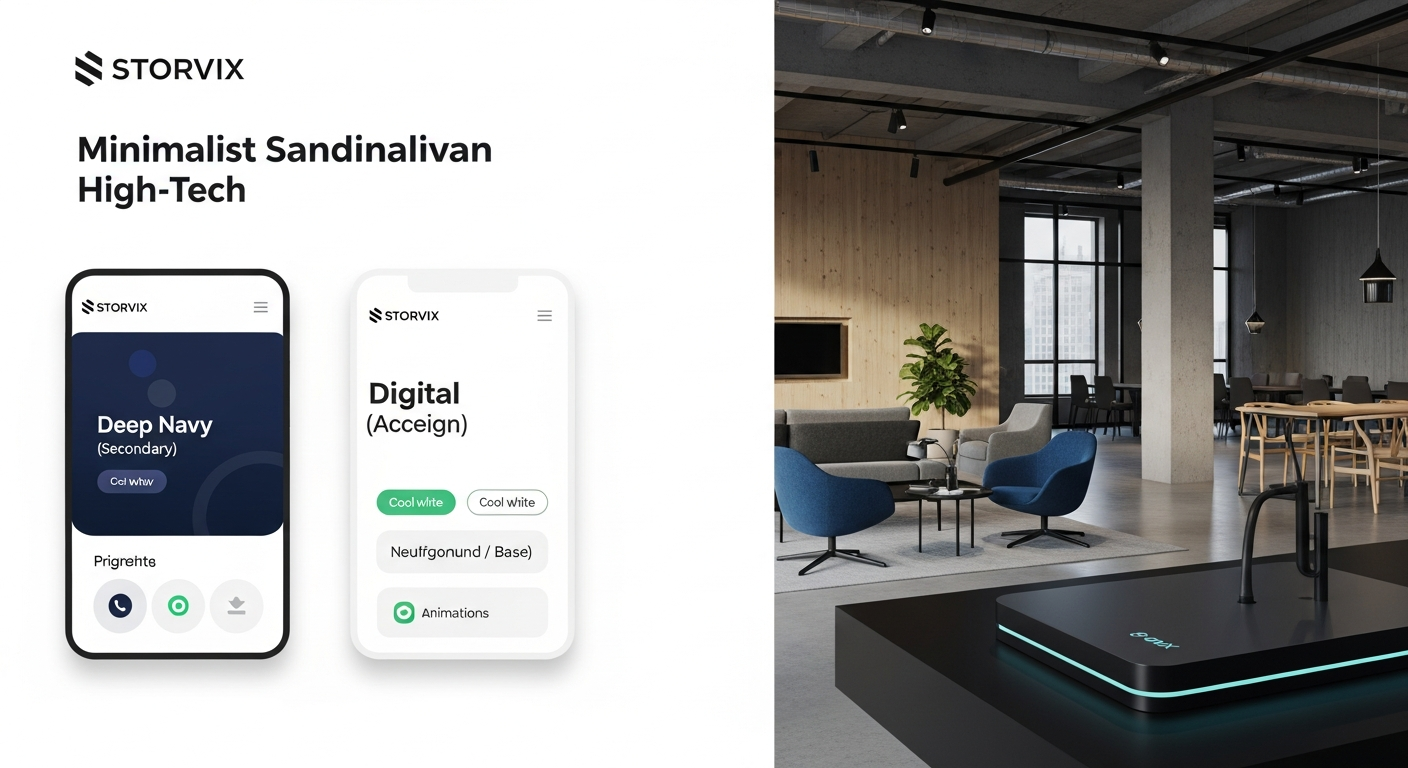
Traditional storage approaches—siloed arrays, manual LUNs, and ad-hoc policies—fail because they were designed for a world of long-lived VMs and operators with time to babysit provisioning. They don’t map cleanly to YAML-driven Kubernetes workflows or offer the policy-as-code controls needed for predictable lifecycle and compliance. The practical strategic shift is to adopt intelligent, Kubernetes-aware data platforms like STORViX that embed lifecycle and governance into the deployment artifacts you already use. This isn’t hype: it’s a control and cost-management story — automated retention, reclaim, snapshot policies, and auditability tied to your manifests, which together reduce risk, lower refresh pressure, and make costs predictable.
Do you have more questions regarding this topic?
Fill in the form, and we will try to help solving it.